The $300 million compliance factory that certified nothing
How two MIT dropouts built a $300 million company on rubber-stamped audits, Indian certification mills, and trust nobody bothered to verify
The certification that everyone trusts and nobody reads
Every time you hand your credit card to a SaaS app, upload medical records to a health portal, or trust a startup with your company’s data, a quiet assumption is doing enormous work in the background. Somebody checked that these people know what they’re doing with your information.
That assumption rests on compliance certifications: SOC 2, ISO 27001, HIPAA, GDPR. If you’ve never encountered these acronyms, you’ve still been protected by them.
Or at least you thought you were.
They’re the security equivalent of the health inspection grade posted in a restaurant window. You don’t read the full inspector’s report. You glance at the letter grade, see an A, and sit down to eat.
SOC 2 (Service Organisation Control Type 2) is the one that comes up most in the software industry. It’s an audit standard developed by the American Institute of Certified Public Accountants. A qualified auditor spends weeks, sometimes months, examining how a company protects data: who can access what, how they handle encryption, what happens when something goes wrong, whether they test their own defences. The auditor produces a detailed report. The company earns a certification. Buyers see the badge and relax.
ISO 27001 works similarly but for a broader international audience. Think of it as a building code inspection: it verifies that an organisation has a proper information security management system in place, from risk assessment to incident response. HIPAA governs healthcare data in the United States, with specific rules about who can see patient records and how they must be stored. GDPR does something similar for the personal data of anyone in the European Union, with famously sharp teeth for enforcement.
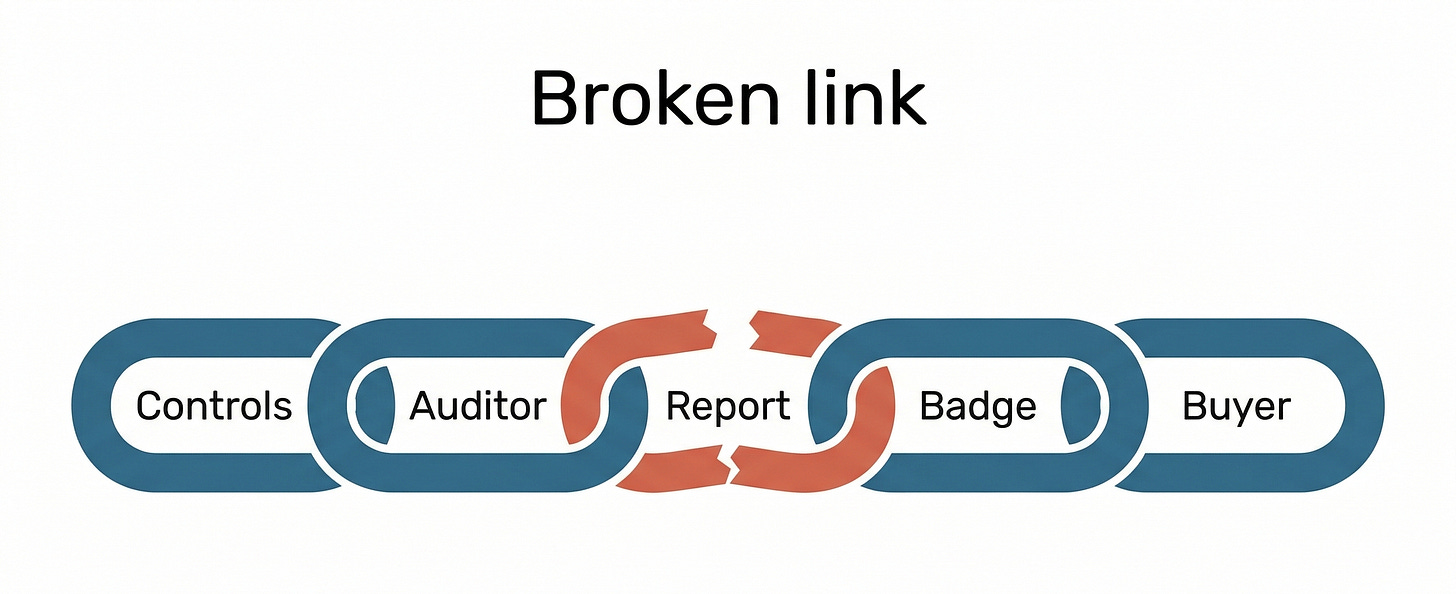
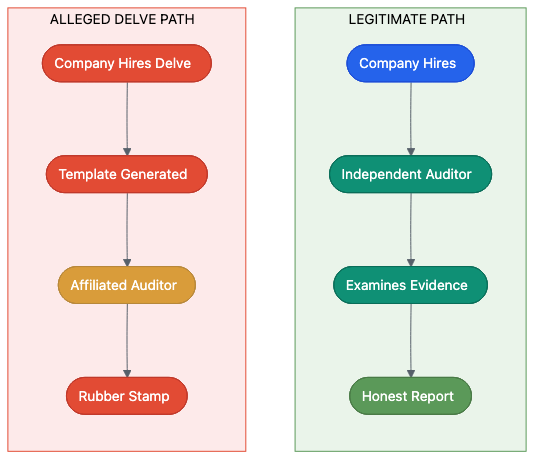
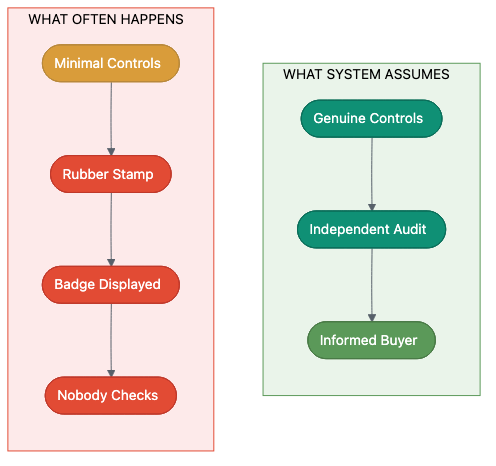
The whole system depends on a chain of trust. Companies hire auditors. Auditors examine evidence. Auditors certify compliance. Buyers trust the certification. Regulators trust the auditors. And almost without exception, nobody in that chain reads the underlying reports.
If you buy software for your company and the vendor shows you a SOC 2 badge, you probably don’t request the full 80-page audit report. If you do request it, you probably don’t read it. If you read it, you probably don’t have the expertise to evaluate whether the controls described are real or theatre.
That gap between trust and verification has existed for years. It was always a vulnerability. In early 2026, someone drove a truck through it.
The company that allegedly exploited that gap was Delve, a Y Combinator-backed startup that promised to make compliance fast, cheap, and painless. According to a forensic investigation published by an anonymous researcher using the pseudonym DeepDelver, Delve’s certifications weren’t worth the PDFs they were printed on.
The investigation’s findings, if accurate, describe one of the most brazen frauds in recent startup history. Not a technical hack or a data breach, but something more basic: the systematic manufacture of fake security certifications for hundreds of companies, many of them handling sensitive health data, financial records, and personal information belonging to millions of people.
From MIT dorm room to $300 million valuation
Delve’s founding story was, until recently, the kind of narrative that venture capital loves to fund and business magazines love to profile.
Karun Kaushik and Selin Kocalar met at MIT. They’d been working on a medical scribe project that required HIPAA compliance (the set of US federal rules governing how healthcare data must be handled). As Kocalar described it on LinkedIn in July 2025:
“The whole experience was painful, complicated, and time-consuming... what stuck with me was the realization that if we struggled this much with compliance, what about every other startup?”
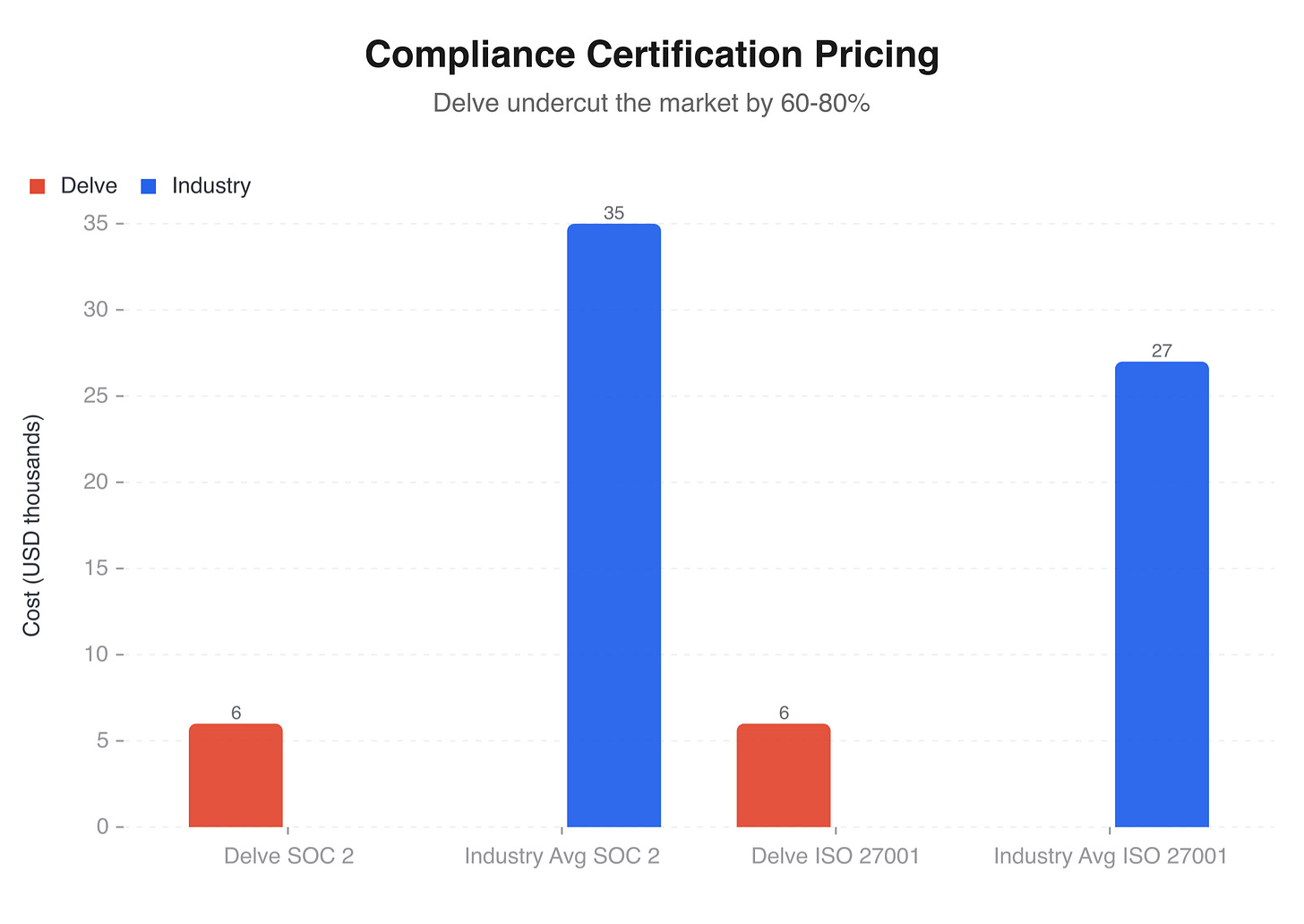
The pain was real and widely shared. For an early-stage startup, getting SOC 2 certified typically costs $20,000 to $50,000 and takes months of work. HIPAA compliance can cost even more. For a two-person company burning through its seed round, diverting that time and money to compliance paperwork feels like paying a tax for the privilege of existing. The founders saw an opportunity: use automation and AI to collapse weeks of audit preparation into days. Make compliance fast. Make it affordable. Make it something founders don’t have to dread.
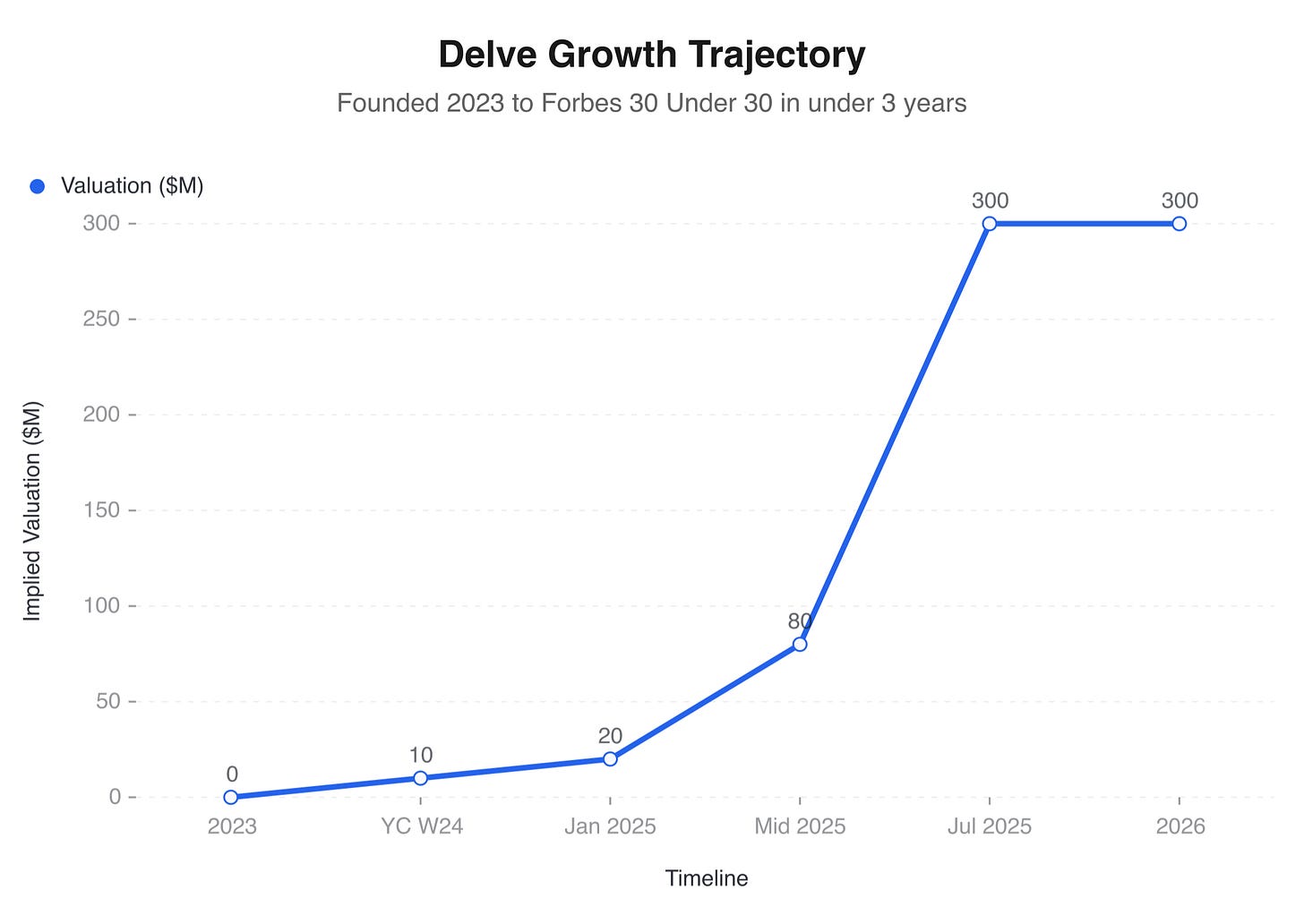
They joined Y Combinator’s W24 batch, one of the most competitive startup accelerators in the world. They raised a $3 million seed round in January 2025. Growth was rapid. By mid-2025, Delve had more than 500 customers, most of them early-stage startups desperate for exactly the kind of fast, cheap compliance Delve was selling.
Then, in July 2025, Insight Partners led a $32 million Series A that valued the company at $300 million. Kaushik told TechCrunch about the market demand: “Compliance frameworks are standardized. Businesses aren’t. That mismatch is why traditional software breaks down.” Kocalar explained how the business had expanded: “As our customer base grew, they started asking for support with other frameworks: SOC 2, PCI, GDPR, ISO, basically the whole alphabet soup of compliance.”
The press coverage was glowing. Two founders, both around 21, had built a company worth $300 million in under two years. Kaushik reportedly made the Forbes 30 Under 30 list for 2026. The story had every ingredient the tech press craves: youth, speed, a real problem, a billion-dollar market, and the implicit validation of Y Combinator and a blue-chip VC firm.
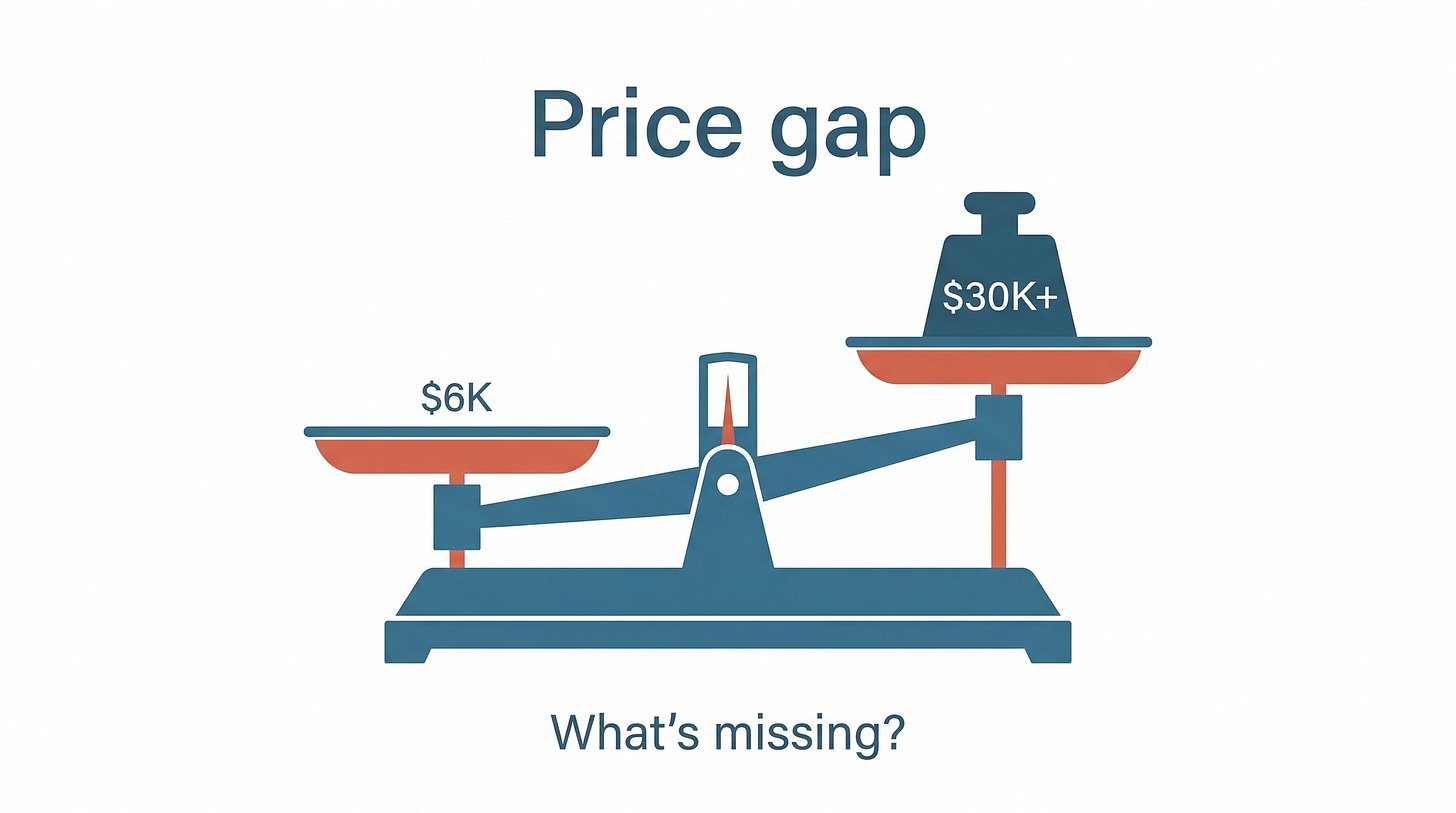
Delve’s pricing was aggressive. According to the DeepDelver investigation, the company had dropped its prices from around $15,000 to roughly $6,000 for SOC 2 certification. At that price point, they were undercutting the market by 60 to 80 percent. Customers flooded in.
Nobody asked the obvious question: how do you run a rigorous security audit for a fraction of the cost and a fraction of the time that every other auditor charges?
The answer, according to the investigation, was simple. You don’t.
The Google Drive link that blew it open
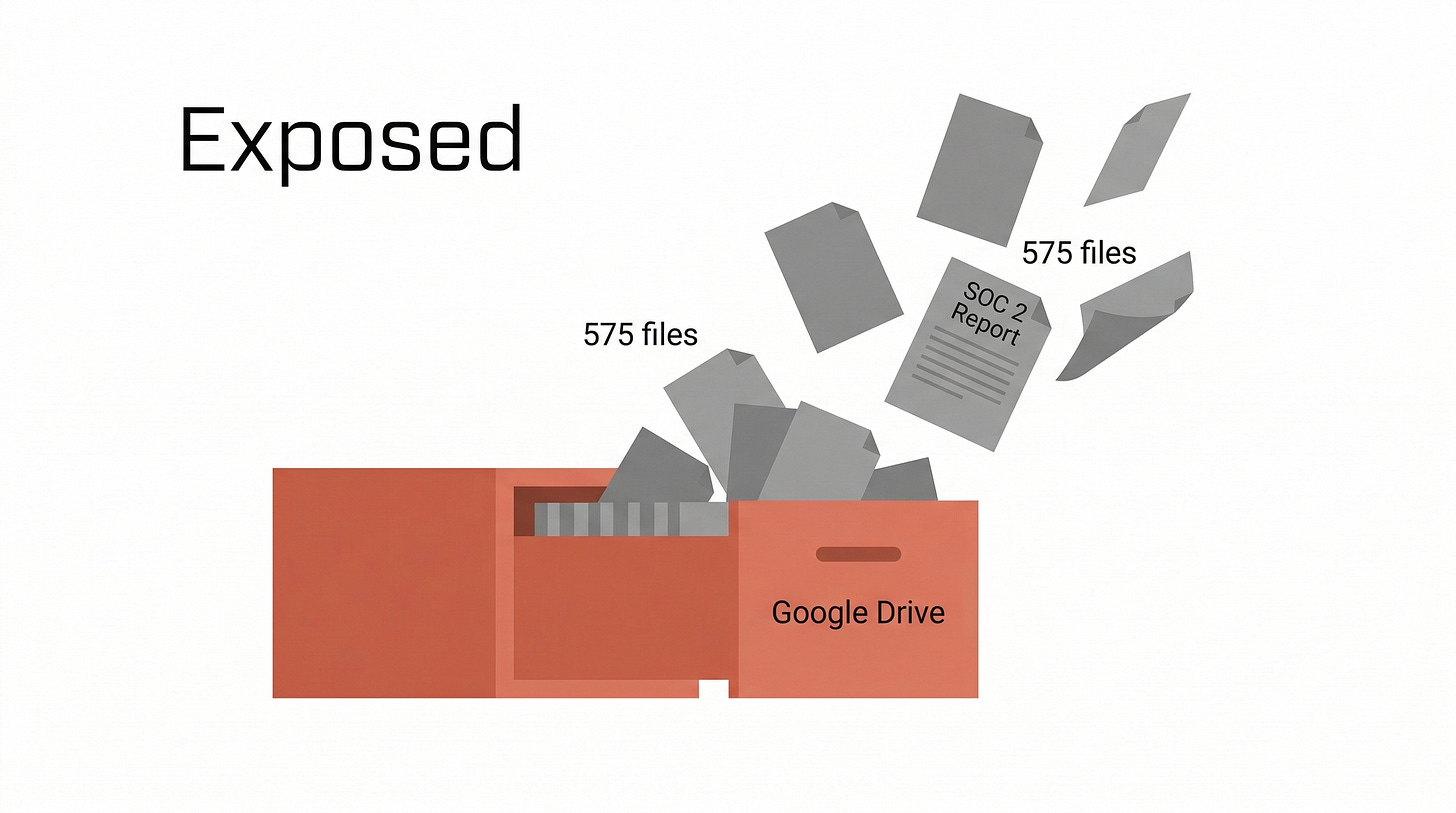
The Delve scandal didn’t surface because of a whistleblower, a data breach, or a regulatory investigation. It surfaced because somebody shared a Google spreadsheet with the wrong permissions.
As DoControl’s analysis put it: “The incident didn’t become public because of a breach, an advanced hacker group, or a whistleblower investigation. It surfaced because an internal Google Spreadsheet was accidentally shared.”
The spreadsheet contained links to 575 confidential audit files: 494 SOC 2 reports and 81 ISO 27001 certifications. Each file belonged to a different Delve customer. Each file was supposed to be a confidential document produced by an independent auditor after weeks of careful examination. And each file was accessible to anyone with the link.
An anonymous researcher, writing under the pseudonym DeepDelver, obtained the files and began a forensic analysis. What they found was extraordinary.
But before the analysis went public, something else happened. Anonymous emails were sent to Delve’s clients, alerting them that their compliance reports might be fraudulent. Delve’s CEO, Karun Kaushik, responded by telling clients the claims were “AI-generated” and represented “falsified claims.” He urged them to ignore the emails.
The DeepDelver investigation then went public. And the evidence it presented was difficult to dismiss as AI-generated fabrication, because the evidence was Delve’s own files.
What 494 reports revealed when someone looked
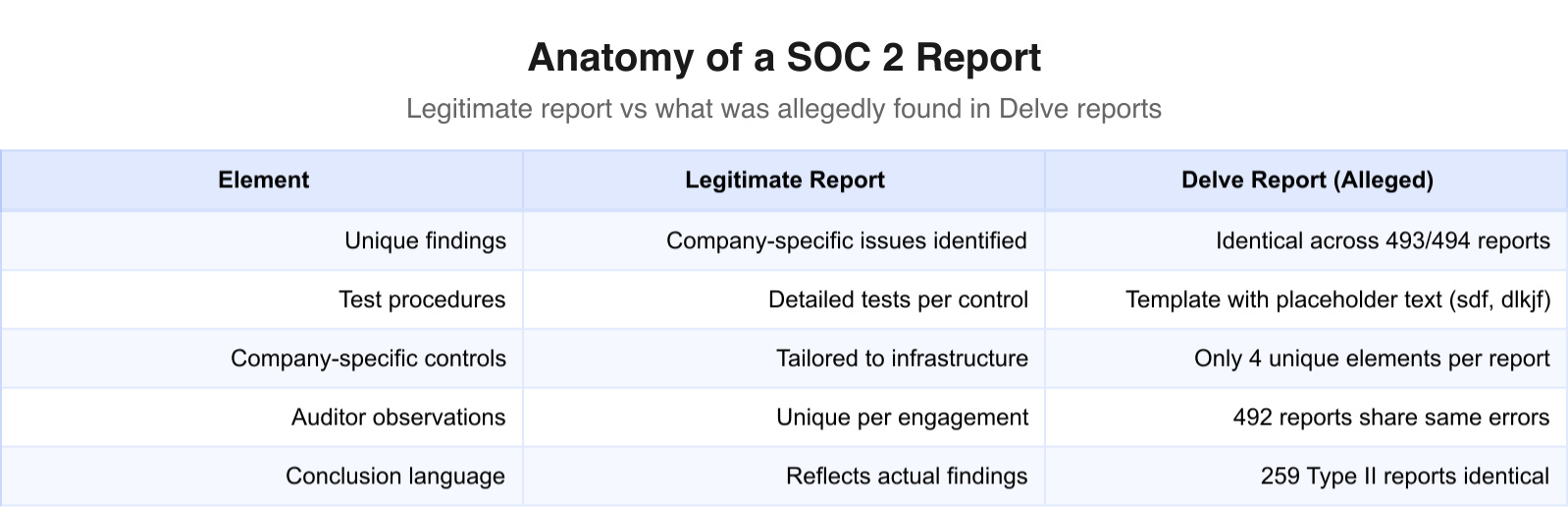
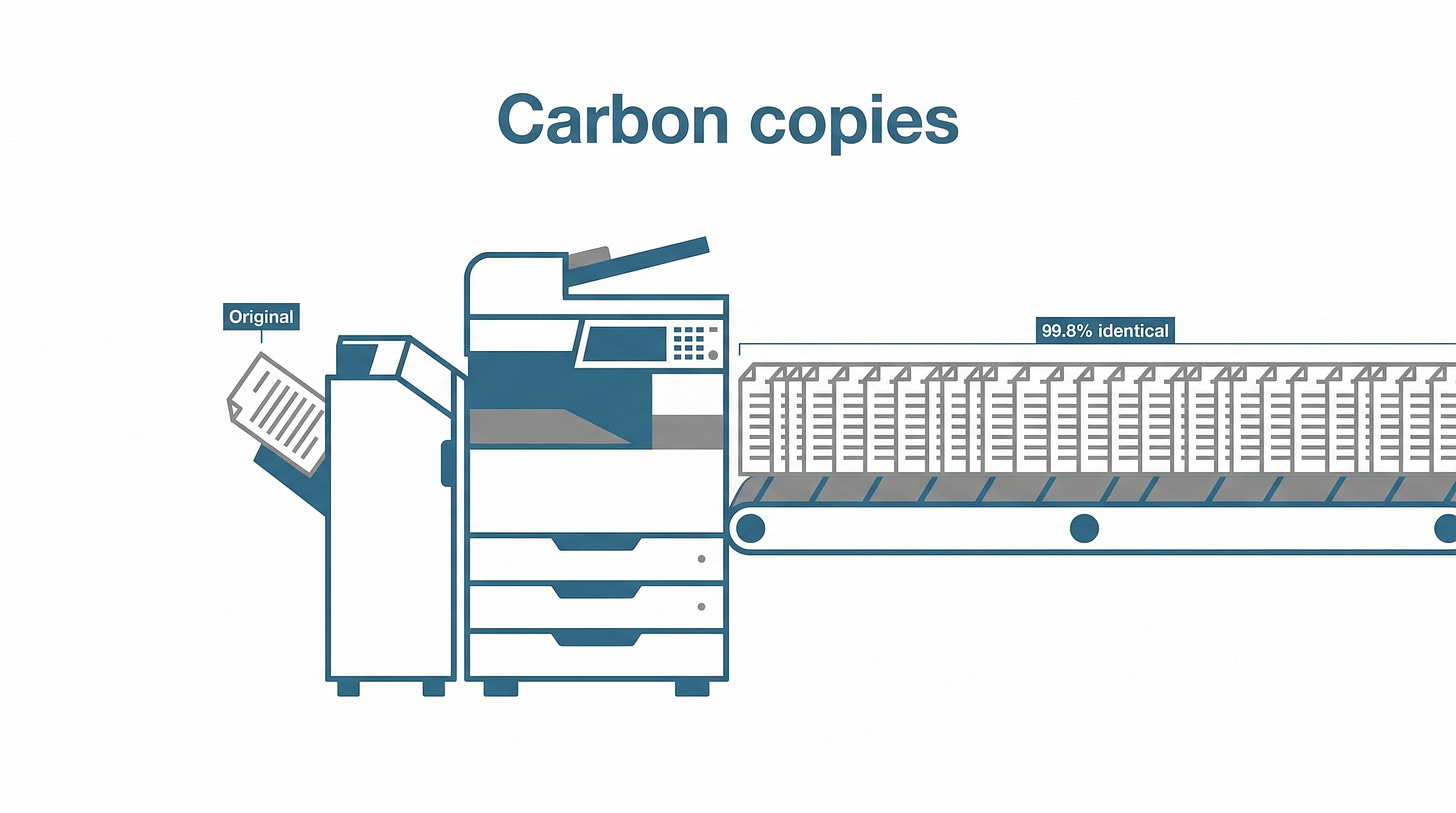
The DeepDelver investigation analysed the 494 SOC 2 reports found in the leaked spreadsheet. The findings, if verified, paint a picture of compliance certification as industrial-scale copy-paste.
Of those 494 reports, 493 contained an identical text string. That’s 99.8 percent. A real SOC 2 audit examines a specific company’s specific security practices, its particular infrastructure, its unique set of employees and processes. No two legitimate audit reports should read like photocopies of each other. These allegedly did.
The similarities went deeper than shared boilerplate. According to the investigation, 492 of the files contained the same grammatical errors, repeated verbatim across reports for hundreds of different companies. When an auditor makes a typo in one report, that’s human error. When the same typo appears in 492 reports for 492 different companies, that’s a template.
According to the DeepDelver analysis, each report contained only four customer-specific elements. Everything else was identical.
Four elements. In a document that’s supposed to represent weeks of detailed, company-specific security examination. To put that in terms of the restaurant analogy: imagine a health inspector visiting 494 different restaurants and producing 494 reports identical except for the restaurant’s name, address, type of food, and number of tables. Same violations noted (or not noted). Same observations. Same conclusions. Word for word.
The 259 Type II reports in the set allegedly contained identical conclusions. A Type II report is supposed to cover a period of ongoing observation, usually six to twelve months, evaluating whether security controls are not just designed properly but operating effectively over time. Each company’s operational period, each company’s set of incidents and changes, each company’s employees and systems would produce different findings. Identical conclusions across 259 companies, covering different time periods for businesses ranging from AI startups to healthcare providers, would be unusual in the extreme.
Then there was the test data. The investigation found what appeared to be keyboard-mashed gibberish in the reports: strings like “sdf” and “dlkjf” in fields where an auditor would normally enter sample data from the company being examined. The kind of placeholder text someone types when they’re filling out a template in a hurry and don’t expect anyone to look closely.
The investigation’s methodology was straightforward: text comparison across hundreds of documents, looking for patterns that would be statistically impossible if each report represented genuine independent analysis. A single shared paragraph between two reports might be coincidence. Near-total identity across nearly 500 suggests something else entirely.
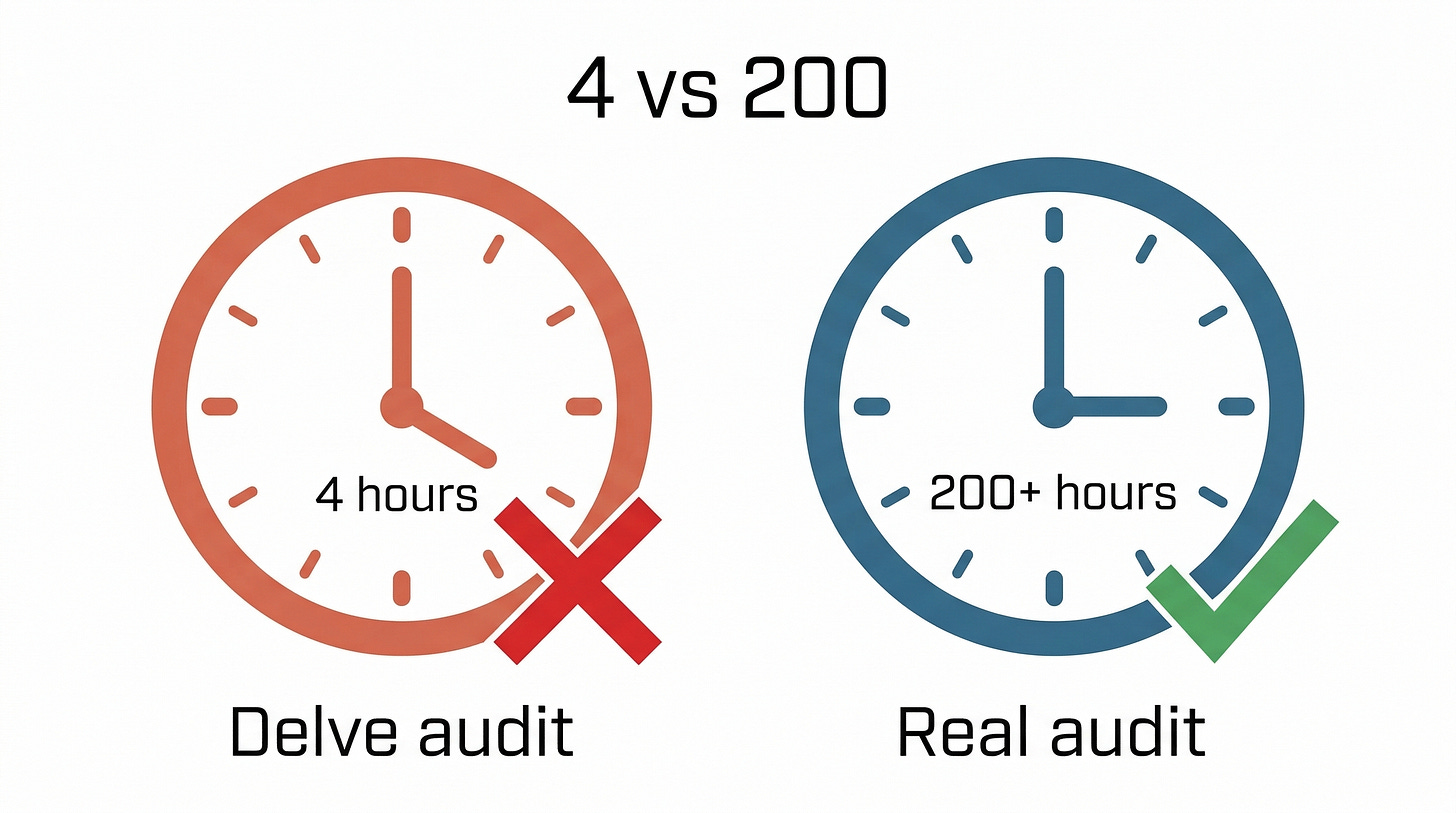
A legitimate SOC 2 Type II audit typically requires more than 200 hours of work, according to industry benchmarks. The investigation found evidence suggesting Delve’s process took roughly four hours of automated preparation plus about two hours per employee. For a 10-person startup, that’s around 24 hours of work producing a report that’s supposed to represent ten times that.
The maths alone should have raised red flags. But the people receiving these reports were startup founders, not audit professionals.
They wanted the badge. They got the badge. They moved on.
The auditors who weren’t what they claimed
A SOC 2 report is only as credible as the auditor who signs it. The DeepDelver investigation identified several auditing firms associated with Delve’s certifications. The three most prominent were Accorp, Gradient Certification, and Glocert. Each, according to the investigation, had qualities that would concern anyone familiar with how legitimate compliance auditing works.
Accorp, according to the investigation, was based in Delhi, India. For a firm signing hundreds of SOC 2 reports for American companies, a Delhi address is unusual. SOC 2 audits are conducted under standards set by the American Institute of Certified Public Accountants, and while there’s no legal requirement that auditors be US-based, the vast majority of established SOC 2 auditing firms operate from North American offices with US-licensed CPAs on staff.
Gradient Certification was registered in Wyoming through a registered agent, a common arrangement for shell companies. Its directors were reportedly based in India. Wyoming is well known in corporate formation circles for minimal disclosure requirements and low fees, making it a popular state for companies that want a US address without a US presence.
Glocert was described as a dormant UK entity.
The pricing these firms allegedly charged tells its own story. According to the investigation, quotes for both SOC 2 and ISO 27001 certifications came in under $2,000. Combined. A legitimate SOC 2 audit alone typically costs $20,000 to $50,000 from an established firm. An ISO 27001 certification runs $15,000 to $40,000. Getting both for under $2,000 would be like getting a full home inspection and a structural engineering assessment for the price of a locksmith visit.
In the legitimate compliance industry, a $2,000 audit is not a bargain. It’s a warning sign. The price tells you exactly how much examination is being done: almost none.
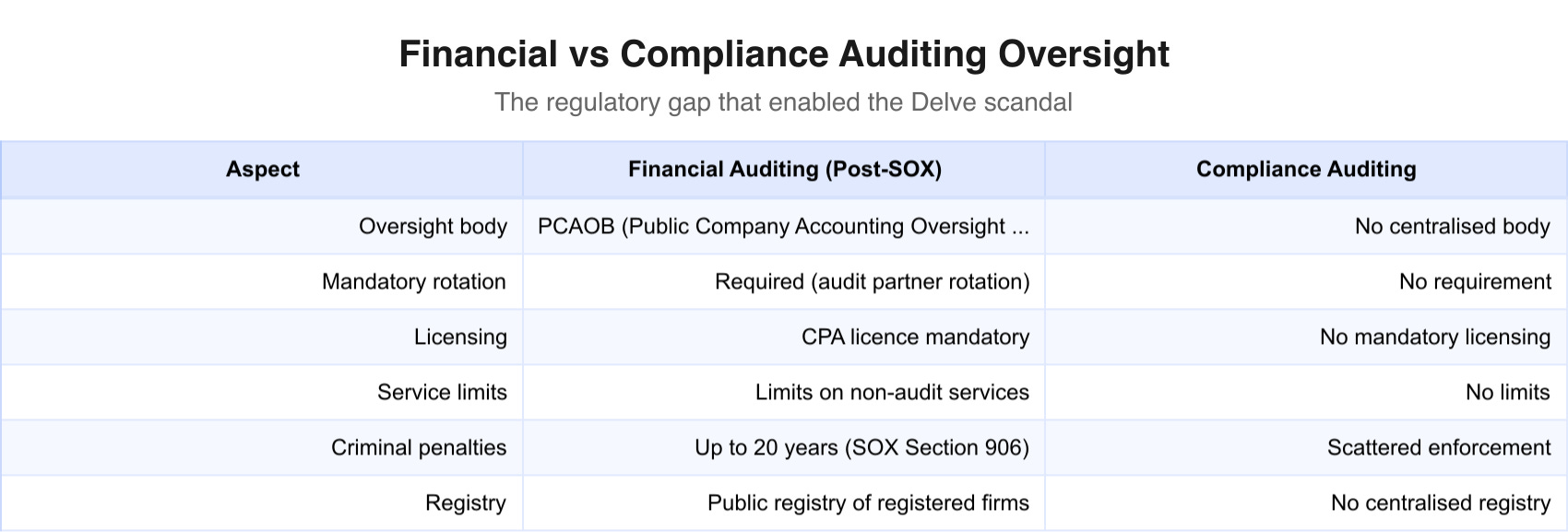
The auditor situation raises a question that extends well beyond Delve. SOC 2 audits are supposed to be conducted by independent third parties. But the system for verifying that independence is remarkably thin. There’s no centralised registry of approved SOC 2 auditors. No mandatory licensing scheme. The American Institute of CPAs sets the standards, but enforcement is scattered across state boards and professional bodies that rarely coordinate.
In practice, this means a compliance startup can partner with auditing firms that exist primarily on paper, produce reports that were generated before the audit began, and present the result to customers who have no practical way to evaluate whether the auditing firm is real, independent, or competent. The trust gap isn’t just between the customer and the compliance vendor. It extends to the entire auditing layer.
Hundreds of companies that thought they were safe
The leaked spreadsheet contained far more than anonymous reports. It included the names of Delve’s customers, and those names read like a cross-section of the modern startup ecosystem.
Among the companies identified in the investigation were Lovable, an AI development platform; Bland, an AI phone calling company; HockeyStack, a B2B analytics platform; Cluely, an AI assistant; and Browser Use, a tool for AI web browsing. The list also reportedly included Duos Edge AI, a publicly traded company on NASDAQ under the ticker DUOT, which raises the stakes considerably beyond the startup world.
Some of these companies handle protected health information (PHI), the category of data HIPAA was specifically designed to safeguard. A fake HIPAA compliance certification for a company handling patient records isn’t an administrative oversight. It means patients’ medical data may have been stored, processed, and transmitted by companies that never underwent genuine examination of their security practices. Every mishandled medical record is a potential HIPAA violation, and every HIPAA violation carries penalties that can reach into the millions.
The investigation found evidence suggesting that Delve’s “trust pages” (the customer-facing dashboards showing compliance status) were generated before the underlying work was done. According to the analysis, 321 out of 322 trust pages examined displayed identical sets of 51 security controls, all showing green checkmarks. The same controls, in the same configuration, for companies ranging from AI chatbot builders to healthcare data processors.
Either every one of those 322 companies happened to implement exactly the same 51 controls in exactly the same way, or the checkmarks were assigned from a template regardless of what controls each company had in place.
A trust page showing all green checkmarks is worth exactly as much as the audit behind it. If the audit was templated, the green checkmarks are decorative.
The investigation also examined Delve’s claimed integrations with other platforms: the technical connections that would allow Delve’s software to pull evidence directly from a company’s infrastructure and verify controls automatically. According to the analysis, most of Delve’s listed integrations did not function as advertised. Only a small fraction of the more than 100 listed integrations were real, the investigation’s figures suggest.
This distinction is important for understanding the nature of the alleged fraud. Legitimate compliance automation platforms like Vanta and Drata connect directly to a company’s cloud infrastructure, pull configuration data, and continuously monitor whether security controls are in place. That’s real automation: software that reads your AWS settings, your access control lists, your encryption configurations. Delve allegedly claimed to do the same thing but, according to the investigation, didn’t have the integrations to pull it off.
The result, if the investigation’s findings are accurate, was a factory. Companies came in. Templates went out. Badges went up. Nobody checked.
The regulatory hammer waiting to fall
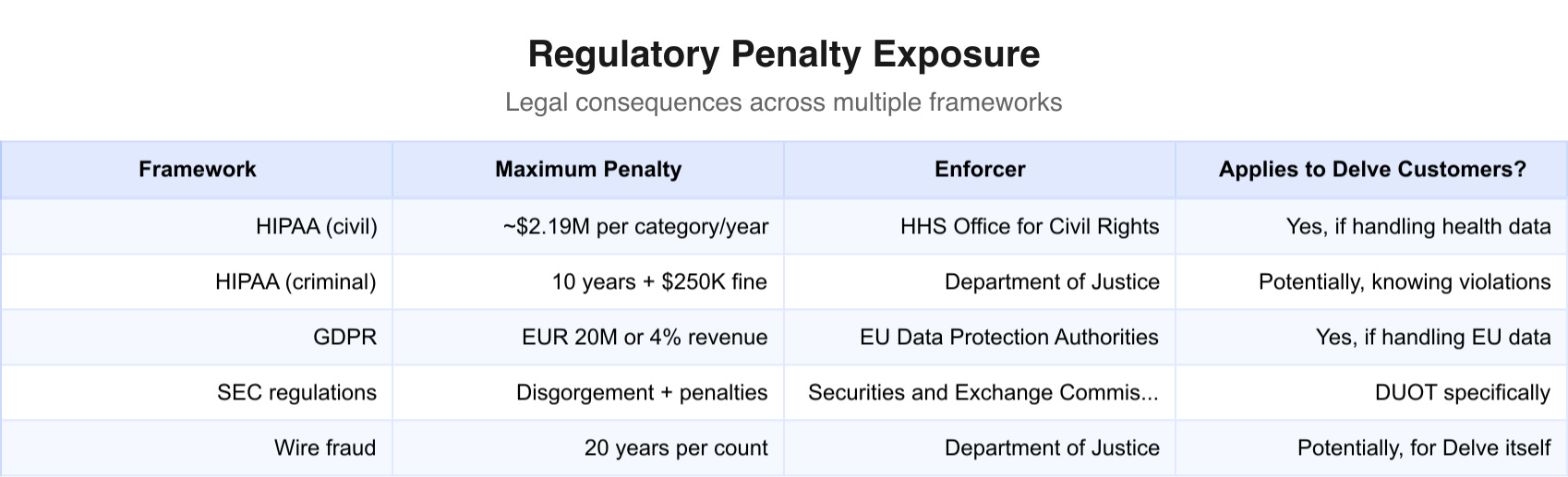
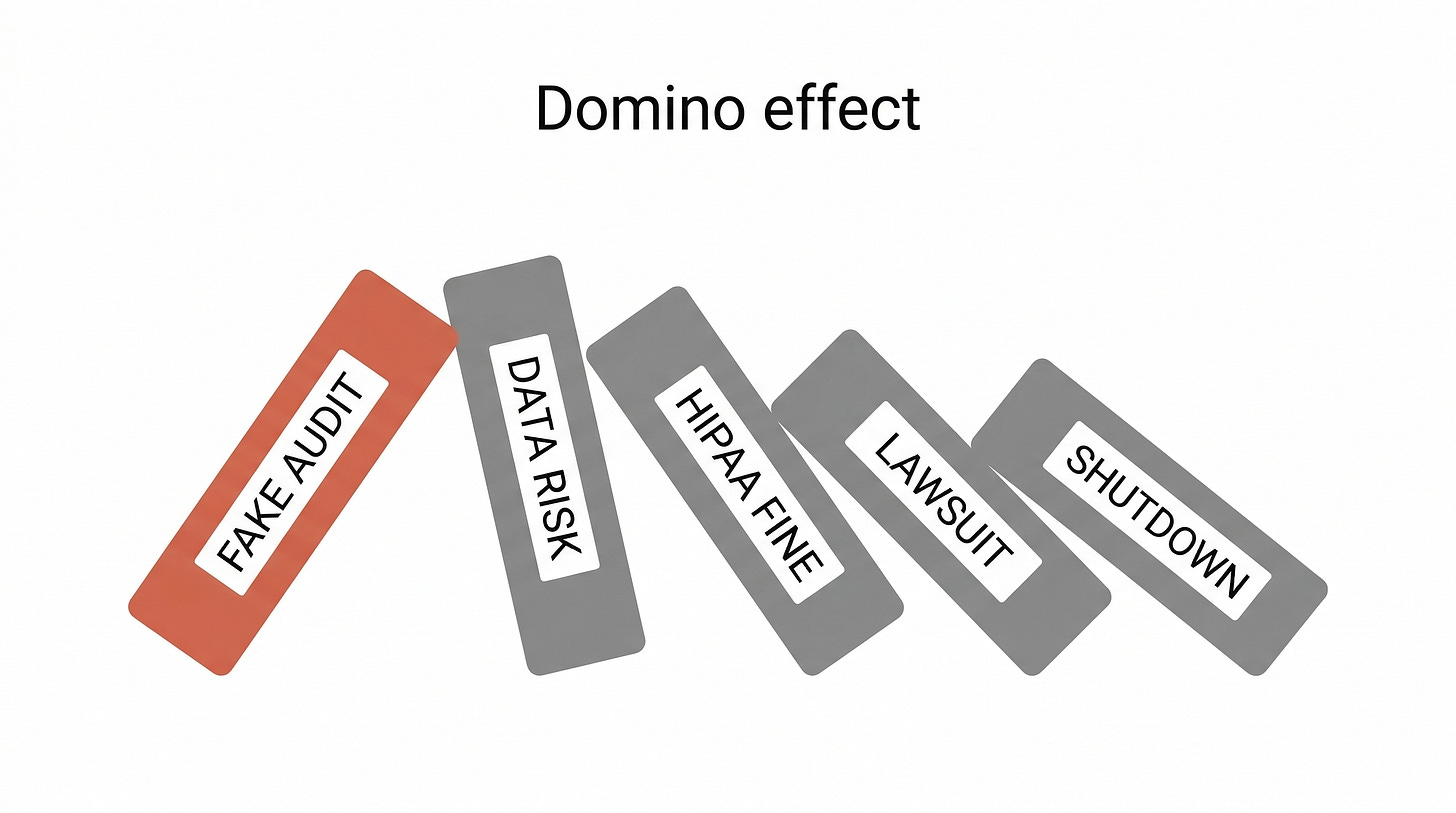
The legal exposure facing Delve and its affected customers is layered, and each layer has its own set of consequences. These are not parking tickets.
Start with HIPAA, the US law governing healthcare data. HIPAA violations are enforced by the Department of Health and Human Services’ Office for Civil Rights. Civil penalties can reach approximately $2.19 million per violation category per year. Criminal penalties, for cases involving knowing misuse of health information, can go up to 10 years in prison and $250,000 in fines.
A “violation” under HIPAA isn’t necessarily one record exposed. It can be a pattern of non-compliance. A company that relied on a fraudulent HIPAA certification and never implemented the controls it claimed to have could face a violation for each category of failure, for each year of non-compliance. If patient data was exposed, the penalties compound.
GDPR penalties for companies handling EU residents’ data can reach up to EUR 20 million or 4 percent of global annual revenue, whichever is higher. If a company obtained a GDPR certification through Delve and that certification was fraudulent, the company’s GDPR compliance was never verified. Every piece of EU personal data processed without genuine compliance represents potential exposure.
For Duos Edge AI (NASDAQ: DUOT), the implications extend into securities regulation. A publicly traded company that represented to investors and customers that it held valid compliance certifications, when those certifications were allegedly fabricated, could face SEC scrutiny. Material misrepresentations about a company’s security posture, even if the company believed the certifications were real, can trigger disclosure obligations and shareholder lawsuits.
Then there’s wire fraud. If Delve knowingly sold fraudulent certifications and used electronic communications (email, online platforms) to do so, that’s potentially federal wire fraud, which carries sentences of up to 20 years per count. With more than 500 customers, the count exposure alone is staggering.
Class action exposure is harder to quantify but easy to imagine. Any Delve customer that suffers a data breach could face lawsuits from its own customers and users. Those Delve customers would, in turn, have claims against Delve for providing fraudulent certifications. The downstream exposure ripples outward. Delve’s customers’ customers, the actual human beings whose data was supposedly being protected, sit at the end of a chain of trust that, according to the investigation, was hollow from the start.
The companies that used Delve’s certifications may be victims. But their customers and users, the people whose data was supposedly being protected, didn’t choose Delve. They didn’t even know Delve existed. They’re the ones holding the risk.
For many of Delve’s startup customers, the legal exposure from a fraudulent certification could be existential. A HIPAA investigation alone, even without a finding of wilful violation, can consume an early-stage company’s entire legal budget. The cost of remediation (getting a legitimate audit, implementing controls that should have been in place from the start, disclosing the situation to partners and regulators) is measured in months and hundreds of thousands of dollars.
For a company that chose Delve precisely because it was trying to save money on compliance, that’s a bitter pill.
When the auditors fail: echoes of Enron and Wirecard
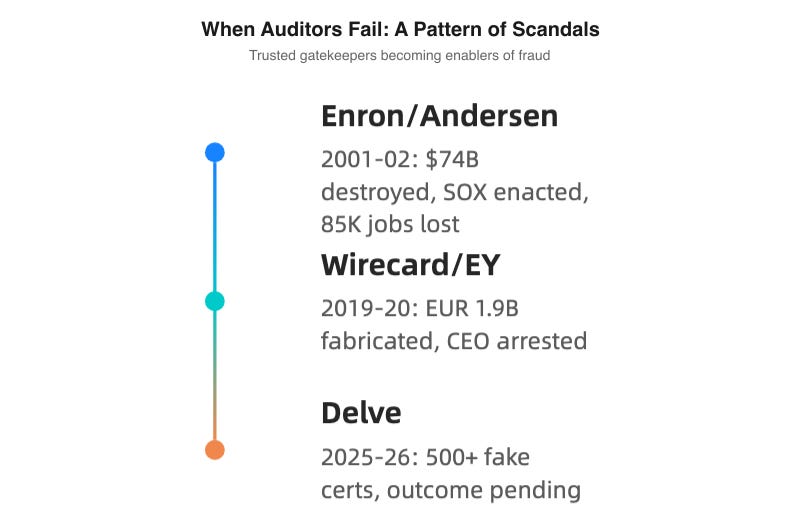
If the allegations against Delve prove accurate, the scandal will join a very specific category in corporate history: cases where the people hired to verify trustworthiness became the mechanism of fraud.
The defining example is Arthur Andersen. In 2001, Andersen was one of the “Big Five” accounting firms, employing roughly 85,000 people worldwide. The firm was Enron’s auditor, responsible for verifying that Enron’s financial statements were accurate. They were not. Enron had fabricated its finances on a massive scale, hiding billions in debt through off-balance-sheet entities. When investigators closed in, Andersen employees shredded documents.
Andersen didn’t survive. The firm was convicted of obstruction of justice (later overturned by the Supreme Court, but too late), surrendered its CPA licences, and effectively dissolved. Eighty-five thousand people lost their jobs. Most were innocent professionals whose firm’s leadership had chosen complicity over integrity. The fallout produced the Sarbanes-Oxley Act of 2002, a sweeping set of reforms to corporate financial auditing that created the Public Company Accounting Oversight Board.
The European parallel is Wirecard. The German fintech company claimed to process billions in payments. Its auditor, EY, signed off on financial statements that included approximately EUR 1.9 billion that didn’t exist. The money was supposedly held in Philippine bank accounts. It was not. Wirecard’s CEO, Markus Braun, was arrested. The company collapsed. EY faced lawsuits and regulatory scrutiny across multiple countries.
The pattern repeats: an entity trusted to verify becomes an entity that enables. The auditor stops being a check on the system and becomes part of the mechanism being checked.
Delve is obviously smaller than Enron or Wirecard. The dollar amounts differ by orders of magnitude. But the structural failure is the same: an auditing function, the very mechanism designed to prevent fraud and assure quality, allegedly became the vehicle for fraud. And in each case, the fraud persisted because nobody upstream bothered to verify the verifiers.
There’s a reason this keeps happening. Auditing is, by nature, a service industry. The company being audited is the same company paying the auditor. That creates a built-in conflict of interest: the auditor’s client is the entity the auditor is supposed to scrutinise. In financial auditing, Sarbanes-Oxley addressed this with mandatory auditor rotation, limits on non-audit services, and independent oversight.
In compliance auditing, no equivalent structure exists. No SOC 2 equivalent of the Public Company Accounting Oversight Board. No mandatory rotation. No centralised registry. No requirement that auditors be independent in any enforceable sense.
The Delve case, if substantiated, will almost certainly reignite calls for compliance auditing reform. The question is whether it will take an Enron-scale disaster, with real data breaches traced back to fake certifications and measurable harm to actual human beings, before regulators act. History suggests that reforms follow catastrophes, not close calls.
The $6,000 audit and the $30,000 audit
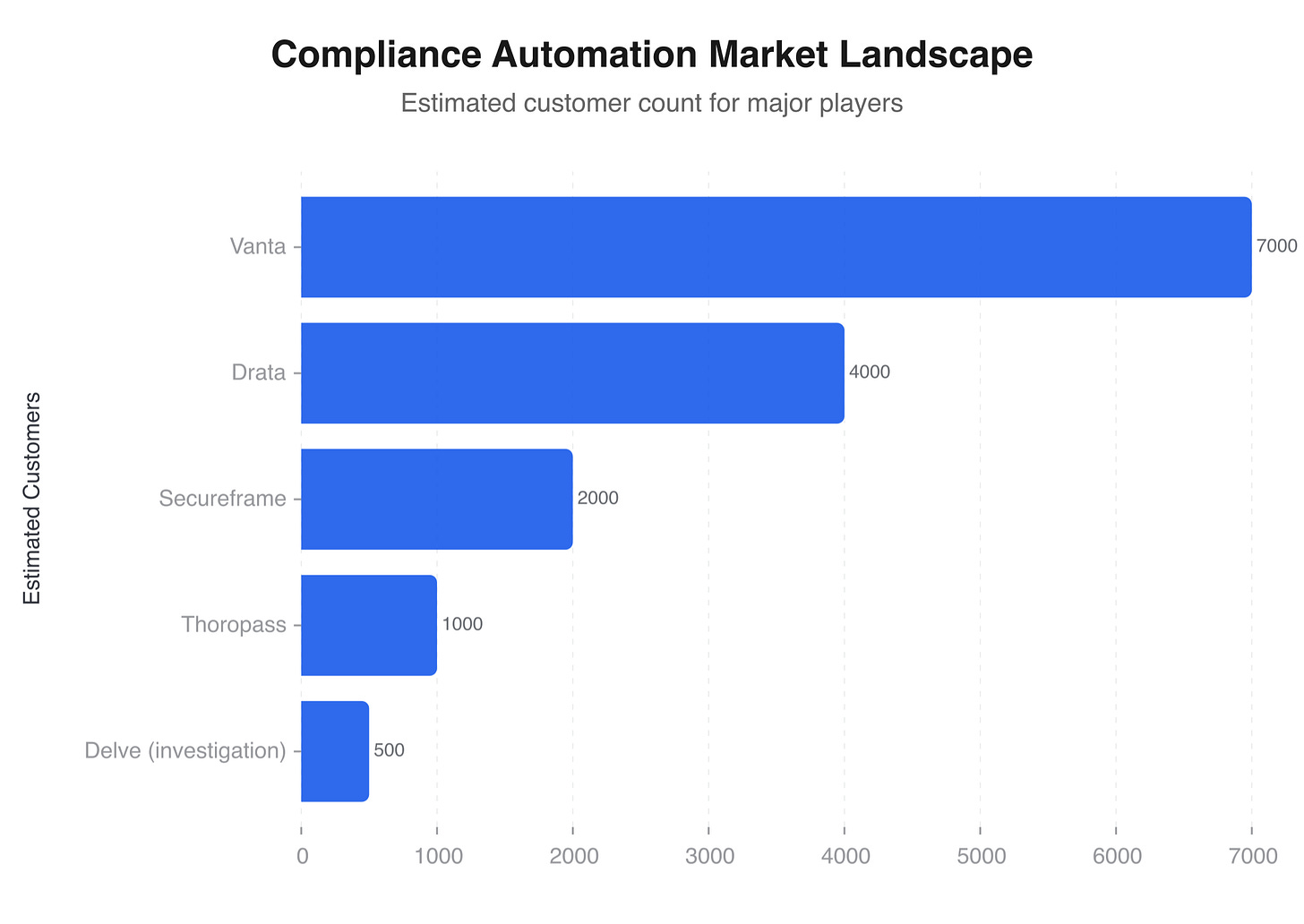
Compliance is a large and growing market. Revenue figures vary depending on who’s counting, but compliance automation software alone is worth tens of billions annually and expanding fast. Every new privacy law, every new data protection regulation, every new industry-specific security requirement creates demand for the tools and services that help companies meet those requirements.
The legitimate players in this market include companies like Vanta, which has raised $150 million and is valued in the billions, along with Drata and Secureframe. These companies sell software that automates the evidence-gathering process for compliance audits. The pitch is real: much of what makes traditional compliance painful is manual evidence collection. Screenshots of access control settings. Spreadsheets documenting who can access what. Logs proving that encryption is enabled. Compliance automation replaces that manual drudgery with software integrations that pull evidence directly from a company’s infrastructure.
The distinction between what these legitimate platforms do and what Delve allegedly did is worth spelling out. Vanta and its competitors automate the preparation and evidence-gathering phase of an audit. They make it easier for companies to organise their documentation, monitor their controls continuously, and present evidence to auditors. But the actual audit, the independent examination by a qualified third party, still happens. The automation makes the process faster and cheaper without eliminating the audit itself.
Delve, according to the investigation, allegedly automated the output rather than the input. Instead of automating evidence collection and presenting it to a real auditor, the company allegedly generated the audit reports themselves, using templates, and paired with auditing firms that would sign off without conducting genuine examinations.
The distinction is the difference between a calculator and a counterfeiting machine. A calculator helps you get the right answer faster. A counterfeiting machine produces something that looks like the right answer but isn’t.
As DoControl wrote in its analysis:
“SOC 2 itself is not broken. The failure here was not the framework, it was how people chose to exploit trust in the process.”
And:
“Automation didn’t cause fraud. Poor incentives, lack of auditor independence, and shortcut-driven compliance culture did.”
Those two quotes capture a tension that will define the compliance industry’s response to the Delve scandal. The frameworks themselves (SOC 2, ISO 27001, HIPAA, GDPR) are sound in their design. SOC 2 controls, properly examined, do provide genuine insight into how well a company protects data. The problem isn’t the standard. It’s that enforcement relies on trust, and trust can be exploited.
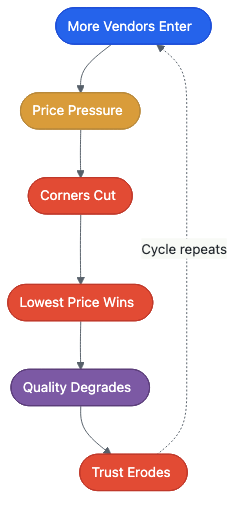
There’s also a structural incentive problem. Startups are price-sensitive. Compliance is perceived as a cost centre, a box to tick on the way to closing an enterprise deal. When one vendor offers SOC 2 certification for $6,000 and another charges $30,000, the startup founder burning through a seed round isn’t going to investigate why the cheap option is cheap. They’ll pick the cheap option and get back to building product.
This price pressure creates a race to the bottom. Vendors who do rigorous work can’t compete on price with vendors who don’t. Customers who can’t tell the difference between a genuine audit and a rubber stamp choose the cheaper option every time. The market rewards speed and affordability, precisely the qualities that, according to the Delve investigation, were achieved by eliminating the audit entirely.
Silence, brigading, and the absence of accountability
As of 20 March 2026, Delve has not issued a public statement addressing the investigation’s findings.
That silence is itself telling. When a company faces allegations of systemic fraud, the standard playbook is to deny, explain, or cooperate. Delve has done none of these publicly. Its initial response, when the anonymous emails reached customers, was to dismiss the claims as “AI-generated” and “falsified.” Since the full investigation was published, with its hundreds of pages of documentary evidence drawn from Delve’s own files, the company has gone quiet.
The response from Delve’s employees, however, has been visible in other ways. According to reports from industry professionals and community moderators, Delve employees have been active in online discussions about the scandal. As one commenter on a CISO-focused forum observed: “Employees from Delve have been brigading posts that speak negatively of them.” Another noted: “No official statement from Delve I can find either... not a good look.”
Brigading (coordinating downvotes or negative responses to suppress criticism) is a distinctly modern form of crisis management. It doesn’t address the substance of the allegations. It tries to make them harder to find. For a company already accused of producing fake reports to create the appearance of security, suppressing online discussion through coordinated voting is grimly consistent: appearance over substance, all the way down.
The investor side is equally quiet. Insight Partners, which led the $32 million Series A at a $300 million valuation, has not publicly commented on the investigation. Y Combinator, which accepted Delve into its prestigious W24 batch and features the company on its website, has not made a public statement.
Their silence is significant because their brands were central to Delve’s credibility. A YC badge and a $32 million round from a major VC firm signal to customers that someone with deep pockets and sharp judgement has vetted this company. That vetting, it appears, may not have included examining the audit reports that were the company’s core product.
The same dynamic that made Delve’s compliance reports persuasive, trusting a badge instead of reading the underlying documentation, also made Delve itself persuasive to investors and customers. YC batch. Insight Partners. $300 million valuation. Nobody read the reports.
The speed with which this story spread through the tech industry suggests it hit a nerve. When tech journalist Erin Griffith shared the story, it reportedly received a million views within hours. Security professionals, CISOs (chief information security officers), startup founders, compliance vendors, and investors all had reason to pay attention. Every CISO who ever accepted a Delve certification from a vendor is now re-evaluating that vendor’s security posture. Every investor who backed a company that used Delve is wondering about their portfolio company’s legal exposure. Every legitimate compliance vendor is watching to see whether the scandal tars the entire industry or isolates the damage to one bad actor.
Your data, their badge, nobody’s guarantee
The Delve investigation, regardless of how the legal proceedings play out, has already exposed a structural weakness in how the technology industry proves it can be trusted with personal data. The system is trust-based, and trust was exploited.
When you sign up for a health app that stores your medical records, you trust that the app complies with HIPAA. When a European user provides their email address to a SaaS tool, they trust that the tool complies with GDPR. When a company evaluates a software vendor and sees a SOC 2 badge on the website, they trust that an independent auditor has verified the vendor’s security controls. Each of those trust decisions happens silently, unconsciously, thousands of times a day, across millions of transactions. And each one rests on a certification that, in hundreds of cases, may have been worth nothing.
What the Delve scandal reveals is that compliance certification has become a checkbox exercise for much of the startup ecosystem. Not because the frameworks are bad, but because the enforcement mechanisms assume good faith at every level of the chain. The company is supposed to implement real controls. The auditor is supposed to verify them independently. The buyer is supposed to review the report. The regulator is supposed to enforce the rules.
When every participant in that chain treats their role as a formality, the entire structure is hollow. It looks solid from the outside. It has all the right logos and badges. But it can’t bear weight.
Several things need to change. None of them are easy.
First, auditor verification needs teeth. A centralised registry of approved compliance auditors, with mandatory licensing, regular quality reviews, and public disclosure of audit outcomes, would make it significantly harder for shell companies in Wyoming to sign off on hundreds of fraudulent reports. The financial auditing world solved this problem (imperfectly) with the Public Company Accounting Oversight Board after Enron. The compliance industry needs its equivalent.
Second, buyers need to read the reports. This is the least popular recommendation and the most necessary one. If you’re evaluating a software vendor that will handle your company’s data, requesting and reading their SOC 2 report should be as routine as checking their pricing page. Most companies don’t do this because they don’t have anyone qualified to evaluate the report. That’s a capability gap worth filling, either with in-house expertise or with third-party review services.
Third, pricing signals deserve scrutiny. When a compliance vendor offers certification at a fraction of the market rate, that is information. It may mean they’ve found genuine efficiencies through automation. It may mean they’ve found efficiencies by eliminating the audit. Asking how a vendor achieves its pricing should be part of due diligence, not just for compliance services but for any service where the quality of the work is hard to observe from the outside.
Fourth, the companies that were Delve’s customers face a fork. They can get legitimate audits, disclose the situation to their customers and partners, and absorb the cost of doing things properly. Or they can hope nobody notices. The first path is expensive and embarrassing. The second is a bet that the downstream consequences of fake certifications (the data breaches, the regulatory investigations, the class action lawsuits) will never materialise. Given the scale of the exposure, that bet looks worse with each passing day.
For ordinary people, the options are more limited. You can’t audit your health app’s SOC 2 report. You can’t verify that your employer’s HR software has genuine ISO 27001 certification. You can’t check whether the AI tool you used last week has real HIPAA compliance or a Delve-generated template.
The system is supposed to do that for you. The Delve scandal suggests that, for at least several hundred companies and the untold number of people whose data they handle, the system didn’t.
The compliance industry will likely survive this scandal. SOC 2 will remain the standard. ISO 27001 will keep its relevance. HIPAA and GDPR aren’t going anywhere. The frameworks are sound. But the question the Delve case forces into the open is one the industry has avoided for years: who audits the auditors?
The answer, right now, is nobody. And until that changes, the badges on the website are worth exactly as much as the faith you’re willing to put in them.
1 The DeepDelver investigation was published by an anonymous researcher using a pseudonym. The use of anonymity in publishing fraud allegations is itself noteworthy; the researcher stated they feared legal retaliation. The investigation’s methodology, based on text comparison across hundreds of leaked documents, has not been independently verified by a third-party forensic analysis firm as of publication.
2 Wyoming requires minimal disclosure for company formation. A registered agent address in Wyoming does not necessarily indicate a shell company, but it is a common structure used to obscure the actual location and ownership of a business entity.
3 Sarbanes-Oxley’s auditor independence provisions include mandatory rotation of the lead audit partner (though not the audit firm itself), restrictions on auditors providing certain non-audit services to audit clients, and requirements for audit committee pre-approval of all services. None of these provisions apply to compliance auditing.